Optus Data Breach Timeline
When events like the Optus Breach take place, it can often be difficult to follow along to all that is taking place, now that it appears to have calmed somewhat, I felt it might be beneficial to share a timeline and some notes I have been keeping of the event since it started on Thursday the 22nd of September.
TLDR:
· Optus suffered a cyber-incident; this was not a ‘sophisticated’ cyber-attack. It was a data breach. Likely on Wednesday 21st September.
· Up to 11.2 million past and present Optus customers are likely impacted.
· The Threat actor responsible for stealing then advertising the data released 10,200 records before claiming to delete the rest of the possible 11.2 million records. Optus did not pay the demanded $1 million USD ransom.
· The fall-out for Optus has been swift and dramatic with customer outrage and government displeasure openly discussed in the media.
· This is Australia’s largest data breach in terms of volume of citizens impacted, with Drivers licenses, Passports and Medicare numbers all difficult to replace.
· Despite the Threat actor claiming to have deleted the data they still had possession for over 7 days so we must assume that all 11.2 million customers data have been exposed.
· This breach will result in ongoing issues for customers involved. Fraud, spam campaigns, phishing attacks and even possible physical impacts are all possible due to the nature of the exposed data.
· Australian organizations and citizens can expect additional attention from cyber criminals in the coming days and weeks as the media attention around Optus continues.
For the timeline I will provide a headline and link for further review, I will include images and comments (in italics) only when they provide situational awareness.
Thursday 22nd September 2022
In the early afternoon the Australian broke the story releasing an article about a cyber-attack at Optus and alleged that over 2.5 million customers data had been stolen.
Optus after the Australian article released a statement on their website about the alleged cyber-attack. This has been updated since Thursday 22nd September.
The current narrative was that this was a ‘highly sophisticated’ attack, and that Optus was unaware of the extend of the exposure of the network by the threat actor.
The OAIC released a statement that Optus had informed them of the breach. At this stage it was anywhere between 2.5 million and 9 million customers impacted.
It was now widely reported across media outlets.
Friday 23 September 2022
The Optus CEO held a press conference with the media and offered a formal apology to the public.
There was considerable customer backlash as customers were not notified prior to the media release on 22 September.
The ACSC released a statement and a ‘what to do next’ for Optus customers.
Optus reported that the hackers used European IP addresses and they could be state linked according to the Sydney Morning Herald.
Essentially whoever stole the data was using a VPN.
The ABC ran a story that an insider at Optus suggested it was human error and that an API was exposed to the internet with no security in place. Optus denied this claim.
It was starting to appear at this stage that Optus had not been impacted by a highly sophisticated attack and had instead been impacted by an opportunistic cyber-criminal.
There was confusion around which data breach this was, after a different user on BreachForums was offering 1.1million Optus customers data for sale on 17th September 2022. This data has now been removed from the forum and was unrelated to the Optus data breach. But it did cause confusion.

Optus starting sending emails to impacted customers.
Saturday 24 September 2022
At around 3am AEST a user on BreachForums, ‘OptusData’ posted that they had stolen 11.2 million customers data from Optus via an exposed API. OptusData was demanding a $1millionUSD ransom in a week or they would start to sell the data.
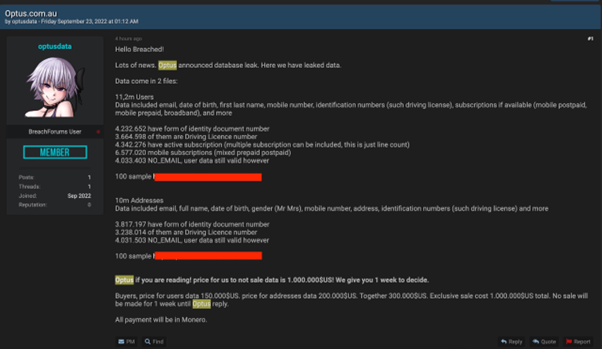
OptusData provided 2 sets of 100 lines of data as initial evidence, on review they appeared legitimate, several email addresses had no matches on Haveibeenpwned and several were ‘no_email8230714@optus.com.au which is reportedly used by Optus as a filler if a customer does not provide an email.
Investigative Journalist Jeremy Kirk went to the effort of asking a neighbor who’s data was in the sample and they confirmed it accurate.
Jeremy Kirk then contacted OptusData who confirmed they had gained access to the stolen data via an unauthenticated API: api.www[dot]http[:]//optus[.]com[.]au
Optus reportedly shut this down, however they have not formally confirmed if this is the avenue of attack as of 28th September.
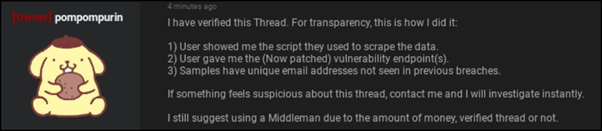
The owner and administrator of BreachForums had also confirmed that the data stolen was legitimate and had ‘verified’ the post, meaning they were vouching for it being real.
Some things were becoming clear at this point.
1, Optus was not attacked by a sophisticated actor, this is a threat actor who is conducting their business on an English Deep Web forum and does not have an alternative means of communication. They appear to be attempting a ransom negotiation in public. These all suggest they are not as sophisticated as Optus suggested.
2, The data stolen looked legitimate and had been verified by researchers and the owner of the forum, who was happy to put their credibility on the line.
3, Australia was about to hit a new level of panic around this data breach.
The AFP reported that they were monitoring the Dark Web for any Optus data that might be posted for sale according to the ABC.
Minister for Home Affairs Clair O’Neill posted a series of tweets about the unfolding situation.
Sunday 25 September 2022
The Department of Home Affairs announced they would introduce new security measures after the Optus breach. Reportedly the new measures would address reporting times of breaches.
Shadow Government Services Minister Paul Fletcher stated that Optus did the right thing “coming out quickly” and advising Australians on the breach of their information.
Monday 26 September 2022
Prime Minister Albanese commented on the breach, calling it a ‘huge wake up call’.
An executive from Optus held a radio interview with 2GB and claimed that Optus had not reviewed the alleged breach data on the forum.
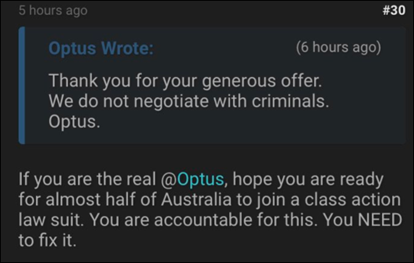
A new user on BreachForums calling themselves ‘Optus’ posted to the thread of OptusData to decline the $1millionUSD ransom stating they ‘don’t negotiate with criminals’. This was not Optus but did frustrate OptusData.
BreachForums was also being flooded with new users who were only adding extra pressure to the situation.
The Minister of Home Affairs declared that the attack was not sophisticated.
Optus announced they would be offering free credit monitoring from Equifax to most high-risk customers.
Tuesday 27 September 2022
OptusData released 10,000 additional users’ data and threatened Optus to pay the ransom, or they would post 10,000 further customers for 5 more days.

Jeremy Kirk reviewed the data and discovered that there were also Medicare numbers present.
Four hours after OptusData posted 10,000 customers data they announced they had deleted the entire data-set and were ending the ransom, they also apologized.

It is unclear exactly why this has taken place, it is possible that OptusData sold the data-set, or they may have been spooked by the interest of law enforcement, their activities and interactions suggested they may have had poor opsec and could be trying to cover their tracks.
However, this is a highly valuable data-set, and they would have no doubt been offered good money for it. It is safe to assume that the entire data-set is still out in the wild and that precautions should be taken accordingly.
Jeremy Kirk did confirm that Optus had told him they did not pay a ransom for the data.

For a comprehensive wrap up of this sequence of events Jeremy Kirk put together an article for bankinfosecurity which is well worth reading.
Unfortunately, other users on BreachForums had already obtained the 10,000 files and reposted them to the forum, regardless of what has happened to the rest of the data the users in this data-set are at highest risk.

There are reports that a class action could be launched against Optus.
Optus customers have received a poor attempt at extortion via text message using the current Optus breach as a lure.
The Australian government has reportedly asked the FBI for assistance.
Australian states are providing guidelines for impacted Optus customers on how to change their license numbers, with Optus planning to reimburse them for costs.
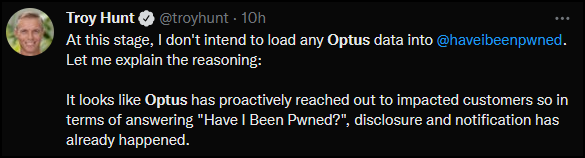
Troy Hunt who owns and runs Haveibeenpwned confirmed that he would not be adding the currently exposed 10,200 customers data due to notification already taking place.
There has been a noticeable uptick in additional Australian data for sale or on offer on BreachForums since the media attention of the Optus breach. Noticeably on Tuesday night there was a school data, old Telstra and NAB data along with over with a 2 million user/password list posted.
Australia is now well and truly front of mind for cyber criminals and all Australian organizations and citizens can expect an increase in cyber-criminal activity for coming weeks.
